Security tips
Are Subscription Tracking Apps Safe?
Subscription trackers can save time and reduce SaaS spend, but they require access to sensitive financial data. This guide explains how these apps work, what “safe” actually means, and how to evaluate risk before connecting your accounts.
8 min. read

TL;DR
Most apps are safe (with caveats)
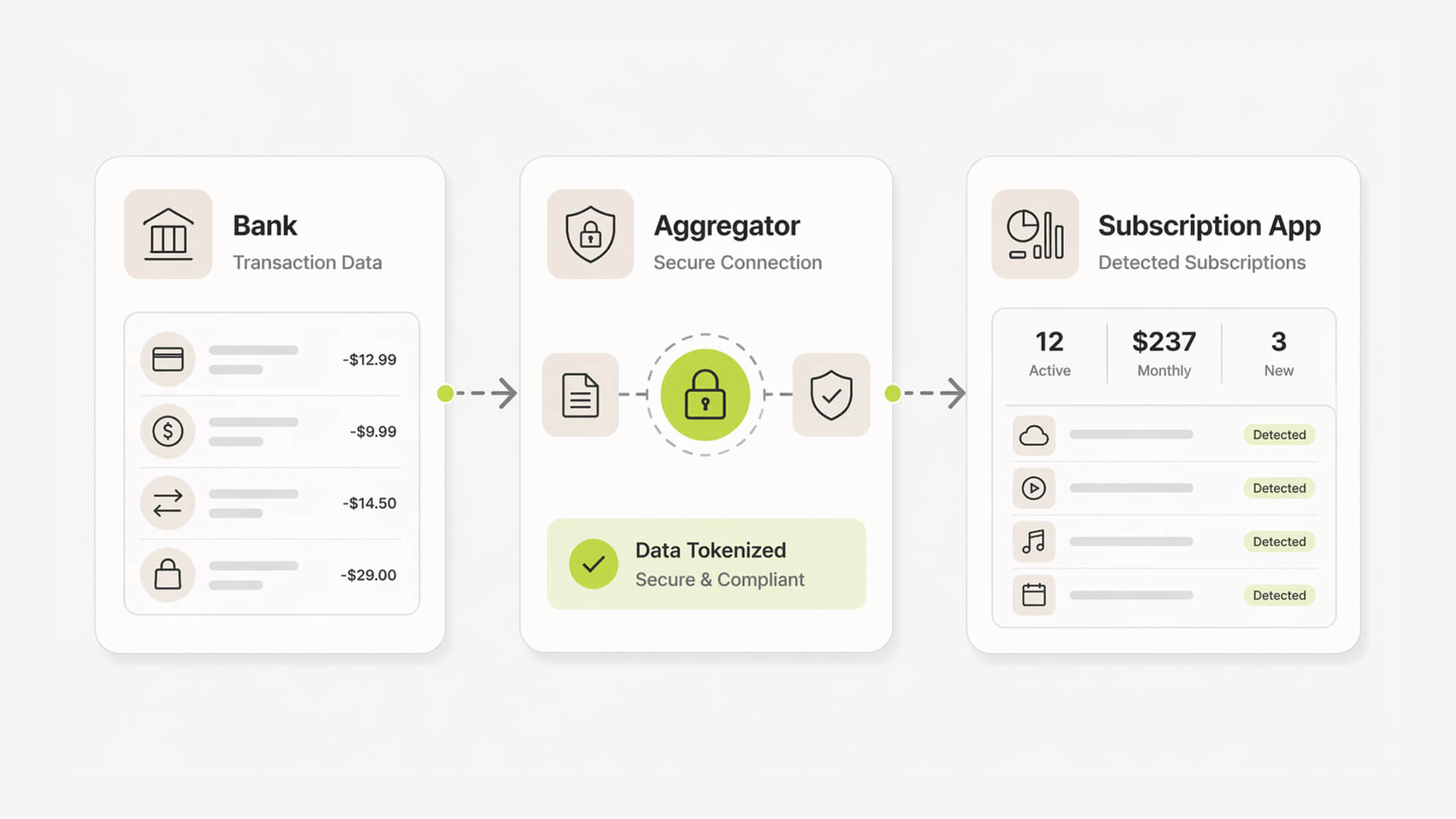
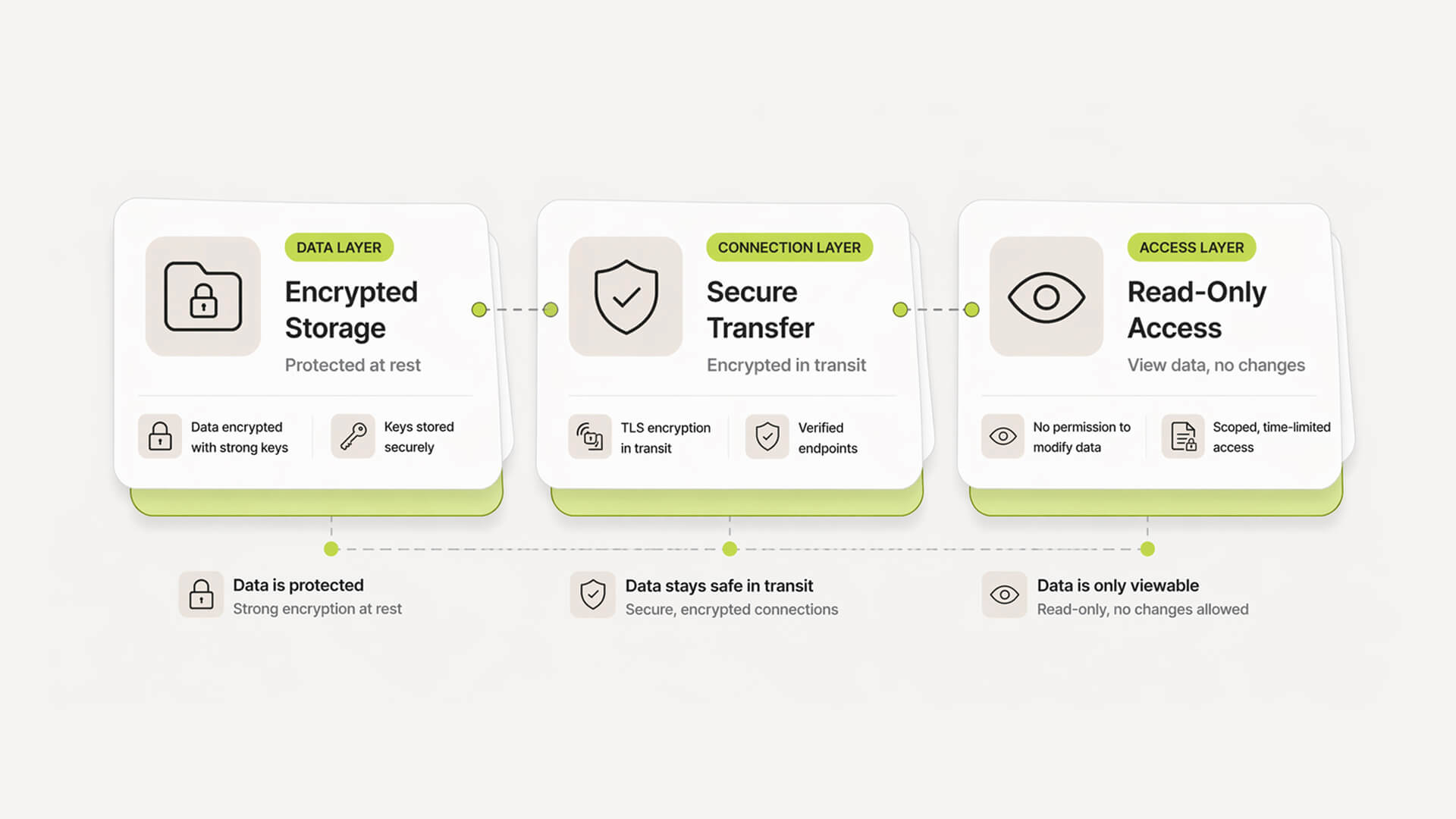
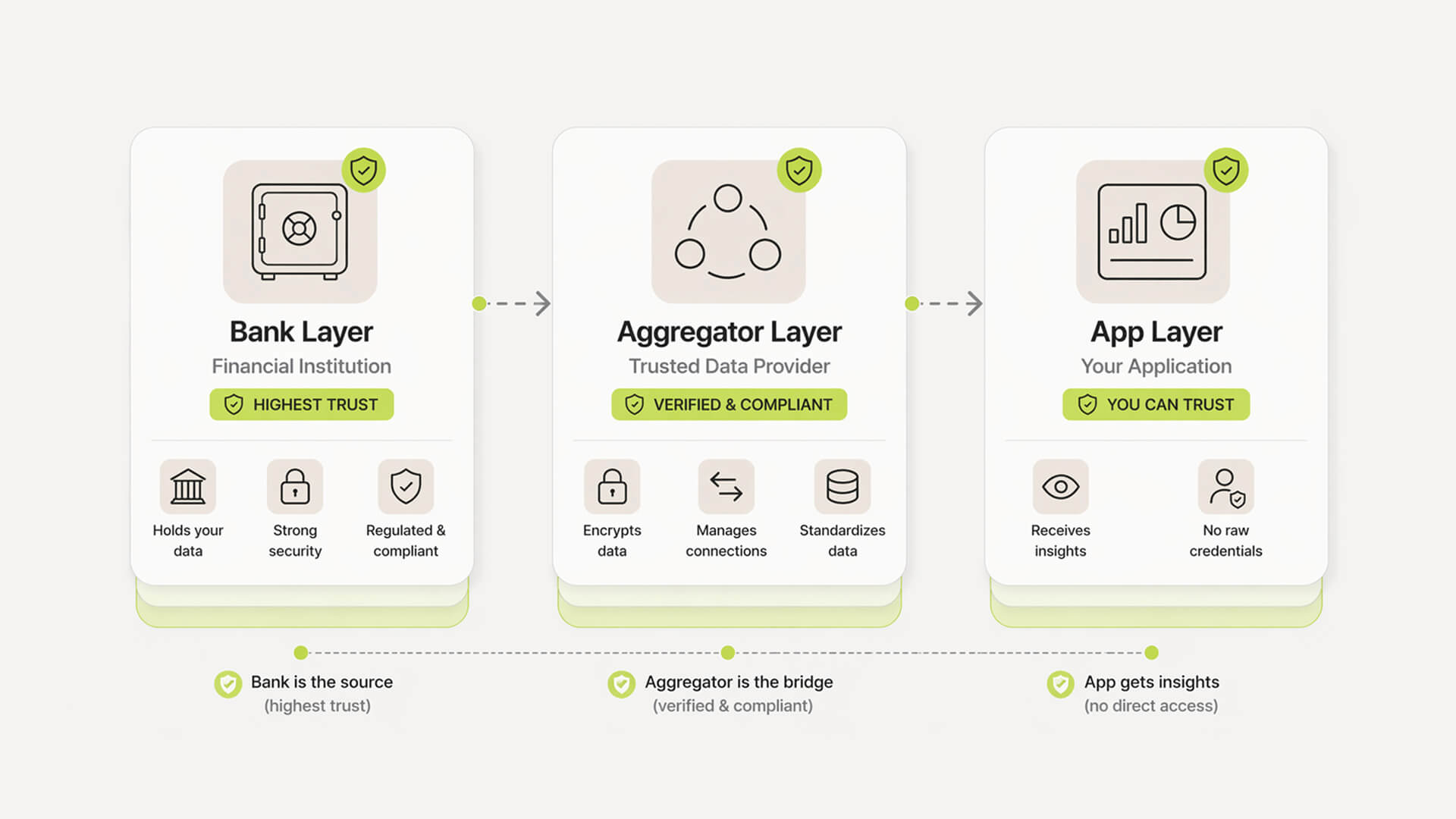
Reputable subscription trackers use encryption and scoped access, but they still sit on sensitive financial data and expand your attack surface, as outlined in subscription app security overviews.
“Read-only” matters
Safe apps cannot move money or initiate payments. They only analyze transaction data through limited permissions.
Risk scales with access
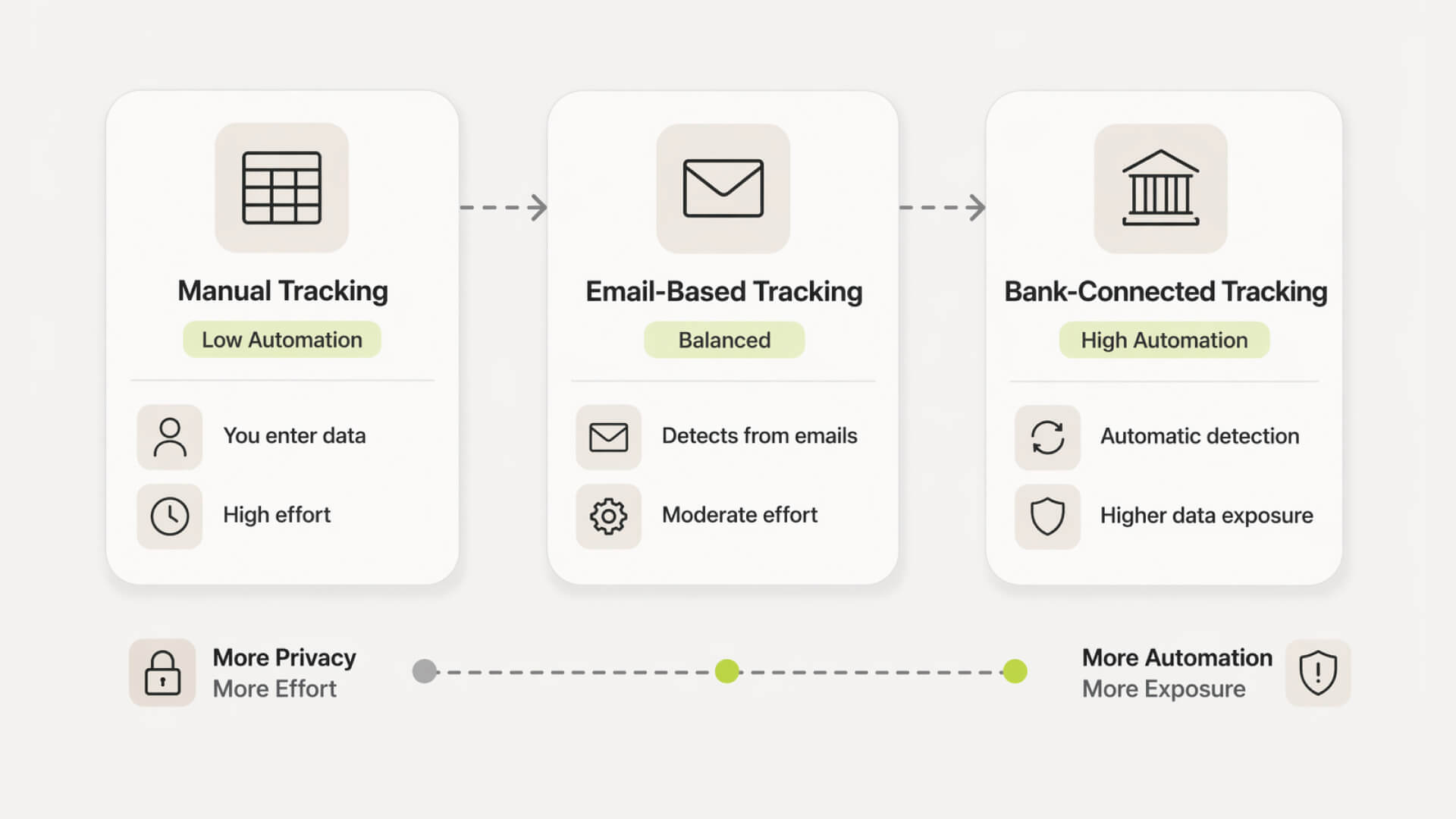
The more you connect, especially bank accounts and email, the more visibility the app has into your financial behavior.
Security signals to check
Look for SOC 2 alignment, encryption in transit and at rest, multi-factor authentication, and clear data handling policies.
Biggest real risk
The concern is rarely direct theft. It is over-collection, profiling, and how your data might be used or shared, similar to concerns raised in how apps collect and use data.
Startup takeaway
These tools can reduce wasted spend quickly, but only make sense if you are comfortable with the level of access required.

Track your SaaS spend
Get full visibility into subscriptions, owners, and upcoming renewals.
Still tracking this manually?
Subsight automatically maps your tools, owners, and renewal timelines in one place.
How to choose a safe subscription tracker (checklist)
Business model transparency
Clear pricing model, not “free” without explanation
Revenue comes from subscriptions, not data resale
No vague claims about “partner insights” or analytics monetization
Privacy policy red flags
Broad language like “may share with partners”
No clear data retention timelines
No mention of deletion or user control
Hard to understand or overly generic policies
Security features to verify
Encryption in transit and at rest
Read-only financial connections
Multi-factor authentication support
Public mention of SOC 2 or similar frameworks
Permission scope evaluation
Only asks for access needed to function
Optional integrations, not forced connections
Clear explanation of what each permission does
Ability to disconnect accounts easily
Exit and data deletion controls
Export your data without friction
Delete account without contacting support
Clear confirmation of data removal
No hidden retention after account closure
For a practical walkthrough, see how to audit your SaaS cost stack in under 2 hours.
Pro Tip: If you are unsure about a tool, start in manual mode or connect a secondary account first. This lets you validate accuracy and behavior before exposing your full financial data. Treat access as something you earn over time, not something you grant upfront.
Why we built Subsight: the subscription tracking trust gap
The old way: blind trust in black-box tools
Most tools ask for access first and explain later. You connect your bank or inbox, and the system starts pulling data without showing exactly what is being accessed or how it is used.
The problem: no visibility into what’s actually shared
For founders, this creates a gap. You gain spend visibility but lose clarity on data exposure. Basic questions become hard to answer, like what is stored, who can access it, and where it flows.
This is especially visible when compared to broader frameworks like what is SaaS management.
The insight: founders want control, not complexity
Early-stage teams do not need enterprise security workflows. They need clear boundaries, minimal permissions, and predictable behavior. The goal is not more data. It is just enough visibility to control spend without introducing unnecessary risk.
The Subsight shortcut
Skip manual audits and spreadsheets
Instead of reconciling transactions line by line, Subsight surfaces subscriptions automatically from read-only data. No need to maintain separate trackers or chase receipts across tools.
This is especially useful for teams trying to reduce waste highlighted in the $50k silent burn.
Automatic subscription detection (without overreach)
Detection is scoped to recurring patterns, not full behavioral profiling. You get visibility into subscriptions without exposing unnecessary financial context.
Owner assignment without extra permissions
Assign responsibility to team members without connecting additional systems. No HR integrations or invasive access required. Keeps accountability simple and contained.
Renewal alerts without inbox access
Stay ahead of renewals without scanning your email. Alerts are based on detected billing cycles, not inbox scraping.
Practical security tips for founders (quick wins)
Account hygiene basics
Use a password manager and unique passwords for every finance tool
Enable multi-factor authentication wherever available
Avoid shared logins across team members
Revoke access for former employees immediately
Permission minimization
Start with the lowest access level and expand only if needed
Avoid connecting both bank and email unless necessary
Review connected accounts regularly and remove unused ones
Be cautious with tools that require full inbox or device access
Monitoring and alerts
Turn on login and activity alerts inside the app
Check bank and card statements weekly, not monthly
Set renewal alerts for high-cost subscriptions
Investigate unfamiliar vendors or unexpected charges quickly
Take control of your SaaS stack
Stop guessing. Know exactly what you’re paying for and who owns it.
Frequently asked questions
Is Plaid safe to connect to my bank?
Can subscription apps access or move my money?
Is manual tracking safer than using an app?
What happens if a subscription app gets hacked?
Do free subscription apps sell my data?
Petras Nargela
Petras is the Founder of Subsight and a veteran entrepreneur with over 10+ years of experience building and scaling digital ventures. Over the past decade, he has co-founded several successful companies that generate 7-figure annual revenue, including a Shopify app studio and a digital agency. Having managed the complex financial stacks of multiple high-growth businesses, he built Subsight to solve the "SaaS leakage" problem he experienced firsthand. He now helps B2B teams turn software chaos into a strategic, automated advantage.